Table of Contents
Enabling single sign-on authentication (SSO) for Azure Active Directory (Azure AD)
Background Info

This article describes step by step instruction of the SSO integration with Azure AD. An additional information about what SSO in Lucy is designed for can be found here.
What preparations need to be done before connecting to Azure AD?
- Upload or create an SSL certificate for Lucy Admin console - see this article.
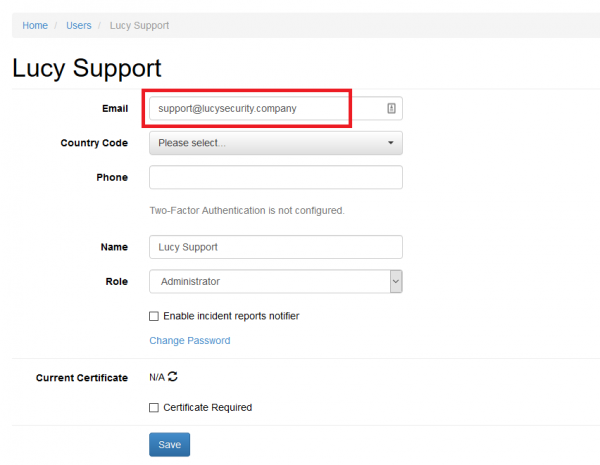
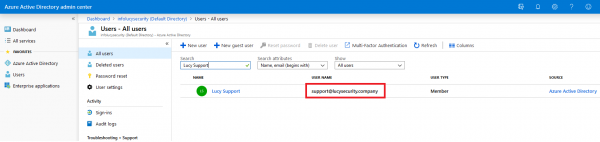
- Make sure you have an Administrator account in Lucy (Settings > Users) with an email address that corresponds to your account in Azure Active Directory. Both accounts must have the same email address:
Enable Single sign-on in Lucy
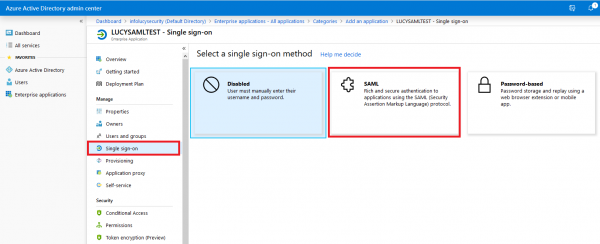
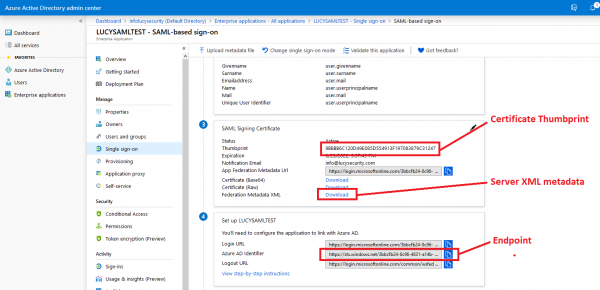
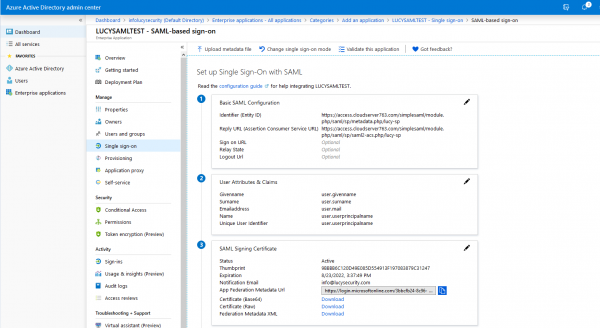
- Configure SAML-based single sign-on to your non-gallery application
Find more about Azure AD Single Sign-on configuration here
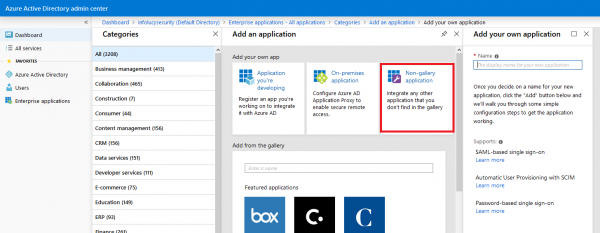
- Add a new non-gallery web app to your Azure AD, see more here
- Open Lucy Admin console
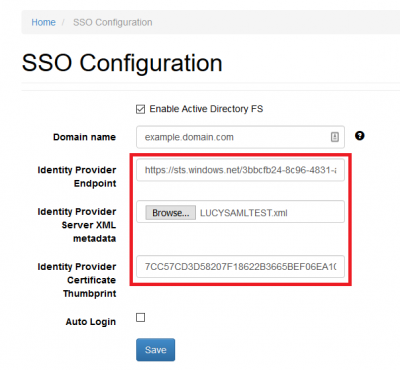
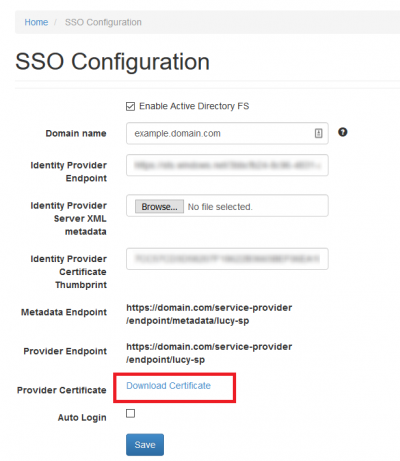
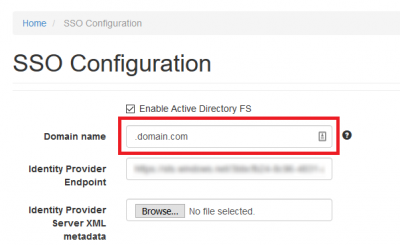
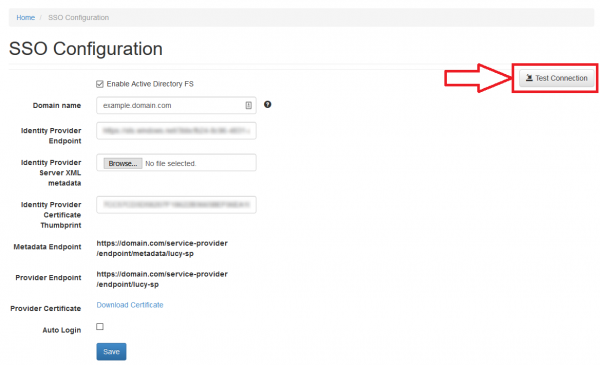
- Navigate to the SSO Configuration page (Settings > SSO Settings)
- Tick the option "Enable Active Directory FS"
- Download the FederationMetadata.xml file from Azure AD and fill the Identity Provider Endpoint and Certificate Thumbprint in Lucy
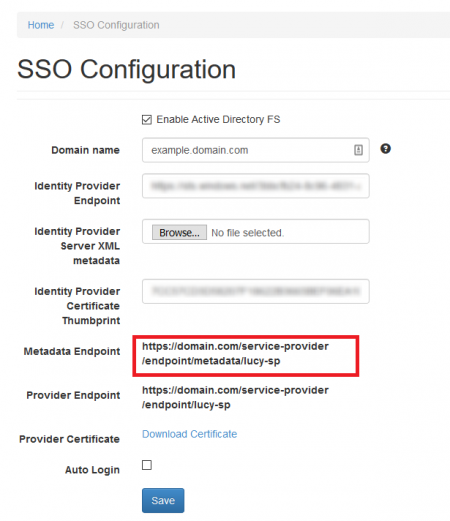
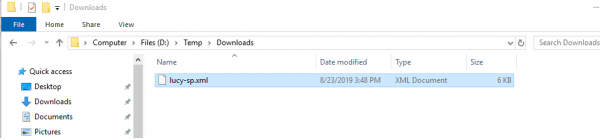
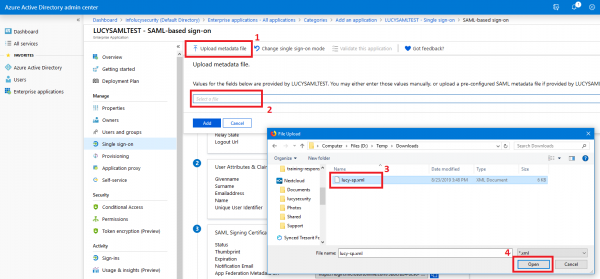
- Download a pre-configured SAML metadata file (copy the URL and paste into your web browser address bar, change the extension of the file to .XML, for example "lucy-sp.xml")
- Upload the pre-configured SAML metadata file
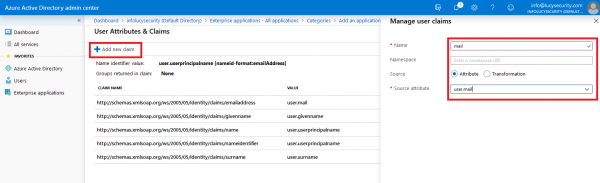
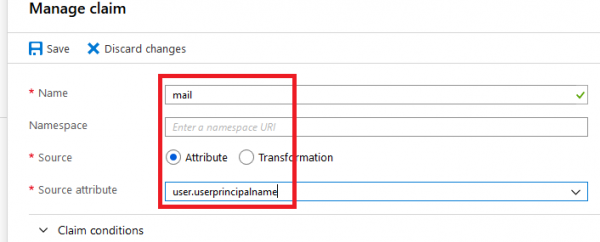
- Add a new Claim "mail" that contain an e-mail address of the user, see more here
Note 
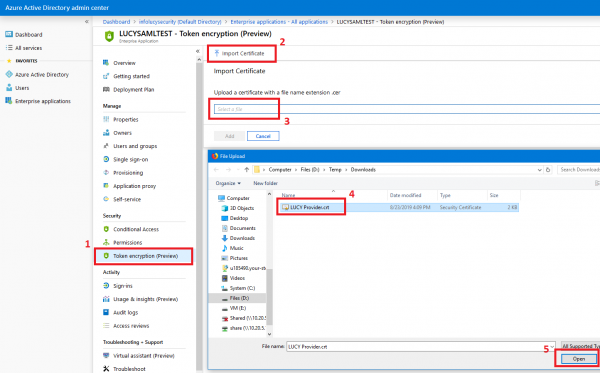
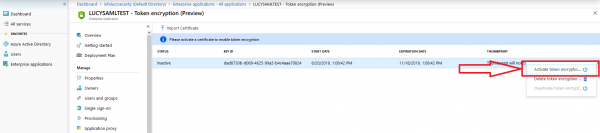
- Configure Azure AD SAML token encryption, see more here

- (optional) You may also configure a domain name that Azure AD will use to receive authentication requests. Azure supports both single domain and range of subdomains, however, for this you need to use a wildcard SSL certificate. By default, Lucy is configured to use system domain.
To enable support for the subdomains, set the value in the Domain field in the following way ".domain.com"
Using wildcard domain name will allow you to use different subdomains in your campaigns.

- (optional) If the option "Auto Login" enabled, Lucy tries to automatically log in using Single Sign-on instead of showing the Login page.
Testing Authentication
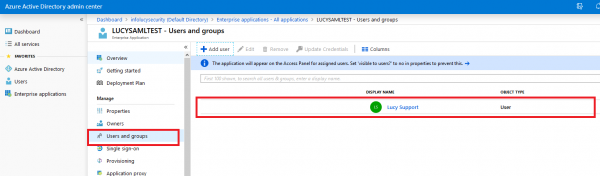
- Make sure you have added users to your app
- Navigate to the SSO Configuration page in Lucy Admin console and click the button Test Connection:
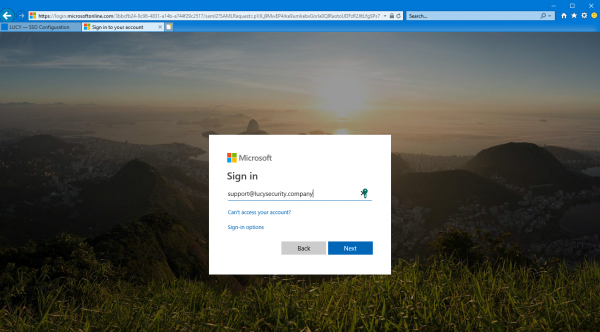
- You will be immediately forwarded to the Microsoft login page. Enter your username and password:
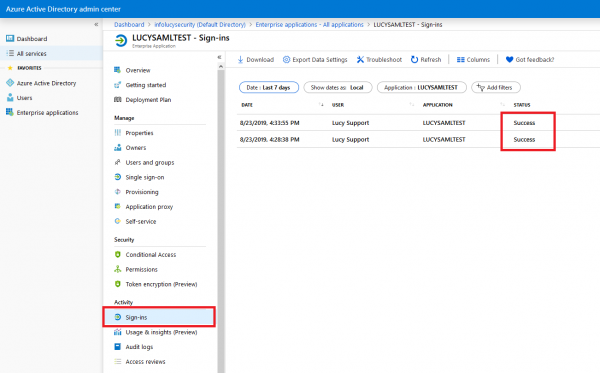
- Once signed in, you will be bounced back to Lucy Admin console. If an error occurs, double-check everything and then check the Sign-ins page within the Activity section for hints as to what could have gone wrong.
OAuth 2.0
The method of authentication is described here.
Troubleshoot problems
- I am redirected back to Lucy's login page after successful authorization through the Single sing-on.
If you are getting back to the login page, try checking the Claim rules (see the section Enable Single sign-on in Lucy, "Add a new Claim 'mail'…"). There must be a claim named "mail", with empty "Namespace" and Source attribute that contains user email address. For example: