Table of Contents
Webfilter and mail filter test
The Email and Internet malware protection test gives you an insight at how your mail server and web proxy handles different variations of test files. You can thus see whether potential malicious code, such as Java files, backdoors, scripts, embedded Office Objects are detected and blocked by the filter infrastructure. Based on these results, you can then carry out targeted phishing campaigns.
With our software you can check which file types could potentially enter the company and which are blocked by the security infrastructure. LUCY works with a wide range of file types that can be brought to the end system via e-mail or on a website for download. You can thus see whether potential malicious code, such as Java files, backdoors, scripts, embedded Office Objects are detected and blocked by the filter infrastructure. Based on these results, you can then carry out targeted phishing campaigns.
Main Questions answered by this tool:
- How can malware potentially enter your network?
- What type of file types can be send as attachments to the end user?
- What type of file types can be downloaded from a website by the user?
- Does your internet and mail protection software detect potential malware?
- Does your internet and mail protection software detect obfuscated malware?
How to perform a mail- and webfiltertest
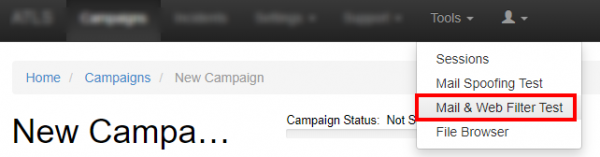
- Step 1: Select the mail & web filter test
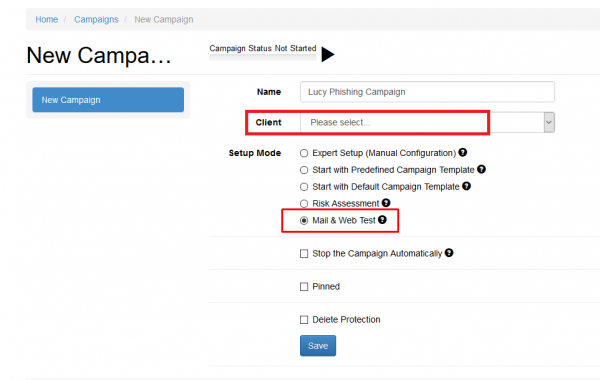
- Step 2: Select a client, make sure the checkbox for the mail- and web filter test is enabled and click save.
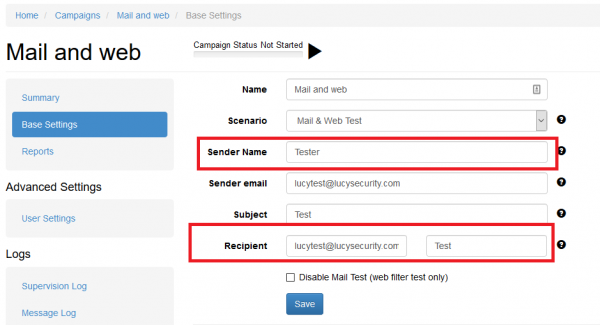
- Step 3: Choose a sender email, from where the mails will be sent. Please choose a sender domain that points to LUCY and where an MX record exists (otherwise the emails will be flagged as spam). Alternatively, you can whitelist the sender domain. However, this only makes sense if the unlocking does not also refer to the mail attachments and lets them through unfiltered. As a recipient choose a mail account on a standard PC from the company you test. The best is to perform this test within a lab/test-pc.
Start with sending a plain text email and verify if it arrives. If the plain text email doesnt arrive, you do not need to proceed to the attachment tests. Try different methods to avoid ending up in spam (Prevent SPAM issues)
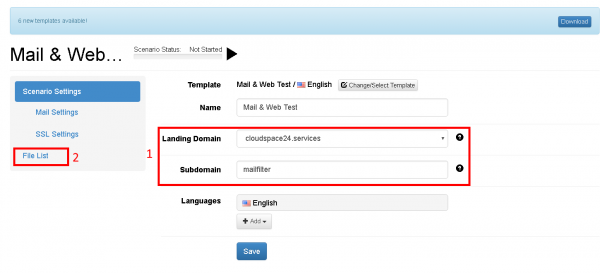
- Step 4: Choose a domain (1), from where the files can be downloaded. Using an IP address is not recommended, as websites which run on IP's are generally blocked on most webfilters. Please use the domain API from LUCY, if you shouldnt have a domain yet. Once you have selected a domain, please click on file list (2)
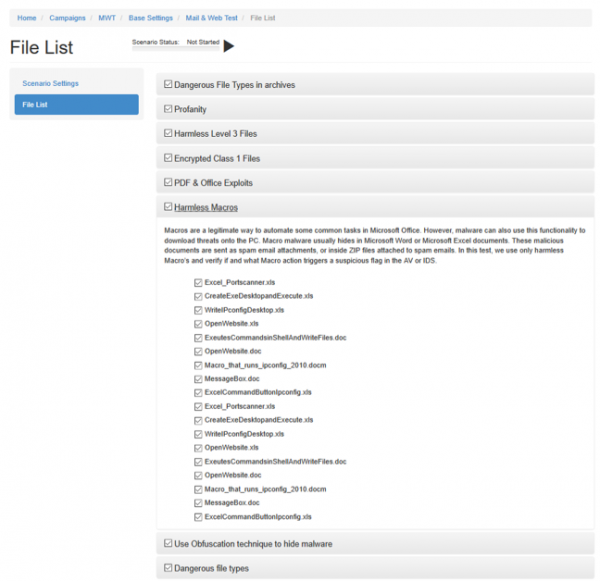
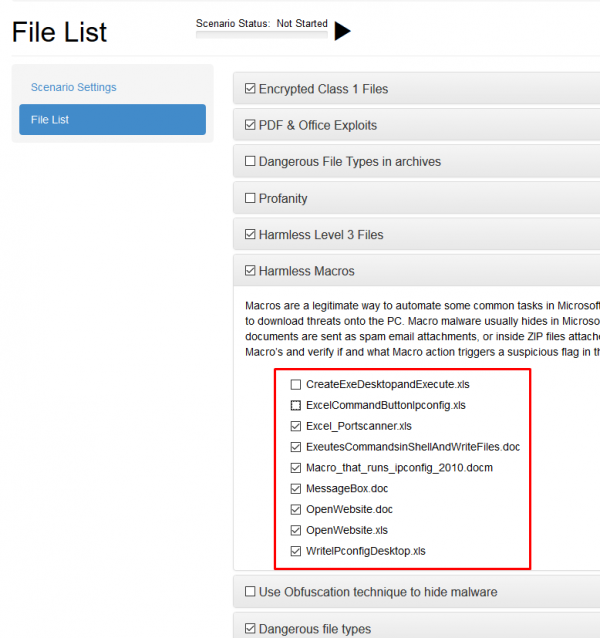
- Step 5: Select the categories you want to mail or download. You can select/deselect categories or single files.
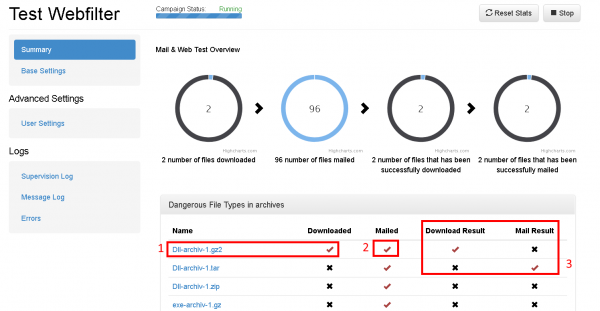
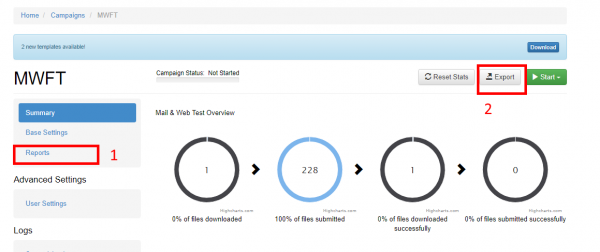
- Step 6: Once you started the campaign, LUCY will send the recipients the selected files. Every file that has been sent will automatically be displayed as sent (2). But you still manually need to verify, if the email actually arrived and the attachement was included. If it was, you can click on the according cross next to the file (3). If you click on the file name (1), you will be able to download the file. Also here: the file shows as downloaded the moment you clicked that link. But you will need to manually confirm (3) that the file actually could be downloaded. As a result you will get a matrix that shows the infrastructure team, what type of code can get mailed and downloaded in a company environment.
How to configure the text of the test categories
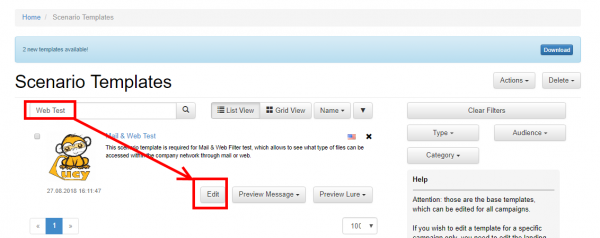
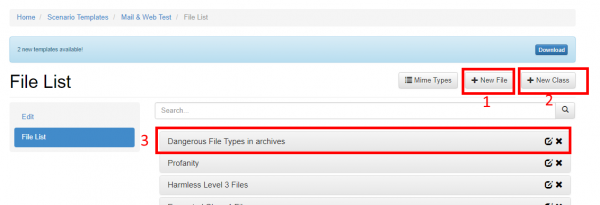
Go to settings –> scenario templates and edit the mail and web filter test template:
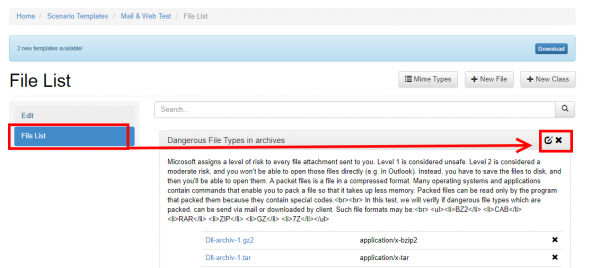
Go to "file list" and then click on the "edit symbol:
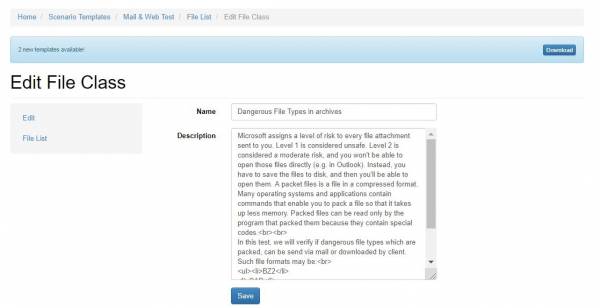
Now you can edit the text of this text class:
Change the payload
How to configure the existing payloads of the tests
- Go to settings –> scenario templates and edit the mail and web filter test template
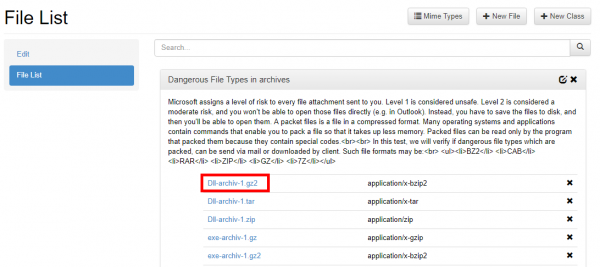
- Go to "file list"
- Click on the link of the file you want to edit:
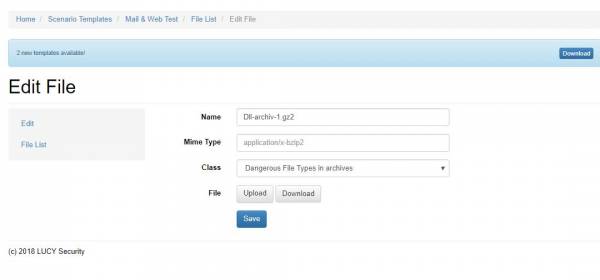
- You can now upload/download the file:
Additional settings
1) Create new file: click on new file 2) Create new class: click on new class 3) Change the order of the tests: select the category, press your left mouse button and move the category in your browser